Заглавная страница Избранные статьи Случайная статья Познавательные статьи Новые добавления Обратная связь FAQ Написать работу КАТЕГОРИИ: ТОП 10 на сайте Приготовление дезинфицирующих растворов различной концентрацииТехника нижней прямой подачи мяча. Франко-прусская война (причины и последствия) Организация работы процедурного кабинета Смысловое и механическое запоминание, их место и роль в усвоении знаний Коммуникативные барьеры и пути их преодоления Обработка изделий медицинского назначения многократного применения Образцы текста публицистического стиля Четыре типа изменения баланса Задачи с ответами для Всероссийской олимпиады по праву 
Мы поможем в написании ваших работ! ЗНАЕТЕ ЛИ ВЫ?
Влияние общества на человека
Приготовление дезинфицирующих растворов различной концентрации Практические работы по географии для 6 класса Организация работы процедурного кабинета Изменения в неживой природе осенью Уборка процедурного кабинета Сольфеджио. Все правила по сольфеджио Балочные системы. Определение реакций опор и моментов защемления |
Text 4. Digital Steganography TechnologyСодержание книги
Поиск на нашем сайте
I.Steganography, which comes from the Greek words "steganos," or "covered" and "graphy," or "writing," can be used to establish covert channels between an insider and one, or more, external entities. Essentially, steganography is used to "cover" the "writing" so as to conceal its very existence. Modern use is called digital steganography.
In April 2006, the National Science and Technology Council released the Federal Plan for Cyber Security and Information Assurance Research and Development, which defines steganography as "the art and science of writing hidden messages in such a way that no one apart from the intended recipient knows of the existence of the message."
Simple steganographic techniques have been in use for hundreds of years, but with the increasing use of files in an electronic format new techniques for information hiding have become possible.
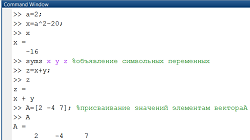
Figure 1 shows how information hiding can be broken down into different areas. Steganography can be used to hide a message intended for later retrieval by a specific individual or group. In this case the aim is to prevent the message being detected by any other party.
The other major area of steganography is copyright marking, where the message to be inserted is used to assert copyright over a document. This can be further divided into watermarking and fingerprinting which will be discussed later.
Steganography and encryption are both used to ensure data confidentiality. However the main difference between them is that with encryption anybody can see that both parties are communicating in secret. Steganography hides the existence of a secret message and in the best case nobody can see that both parties are communicating in secret. This makes steganography suitable for some tasks for which encryption isn’t, such as copyright marking. Adding encrypted copyright information to a file could be easy to remove but embedding it within the contents of the file itself can prevent it being easily identified and removed.
Figure 2 shows a comparison of different techniques for communicating in secret. Encryption allows secure communication requiring a key to read the information. An attacker cannot remove the encryption but it is relatively easy to modify the file, making it unreadable for the intended recipient.
Digital signatures allow authorship of a document to be asserted. The signature can be removed easily but any changes made will invalidate the signature, therefore integrity is maintained.
Steganography provides a means of secret communication which cannot be removed without significantly altering the data in which it is embedded. The embedded data will be confidential unless an attacker can find a way to detect it.
II.Attacks Information hiding techniques still suffer from several limitations leaving them open to attack and robustness criteria vary between different techniques. Attacks can be broadly categorized although some attacks will fit into multiple categories.
Basic Attacks: Basic attacks take advantage of limitations in the design of the embedding techniques. Simple spread spectrum techniques, for example, are able to survive amplitude distortion and noise addition but are vulnerable to timing errors. Synchronisation of the chip signal is required in order for the technique to work so adjusting the synchronisation can cause the embedded data to be lost.
It is possible to alter the length of a piece of audio without changing the pitch and this can also be an effective attack on audio files.
Robustness Attacks: Robustness attacks attempt to diminish or remove the presence of a watermark. Although most techniques can survive a variety of transformations, compression, noise addition, etc they do not cope so easily with combinations of them or with random geometric distortions. If a series of minor distortions are applied the watermark can be lost while the image remains largely unchanged. What changes have been made will likely be acceptable to pirates who do not usually require high quality copies. Since robustness attacks involve the use of common manipulations, they need not always be malicious but could just be the result of normal usage by licensed users.
Protecting against these attacks can be done by anticipating which transformations pirates are likely to use. Embedding multiple copies of the mark using inverse transformations can increase the resistance to these attacks. However, trying to guess potential attacks is not ideal. The use of benchmarking for evaluating techniques could help to determine how robust the technique is. StirMark is a tool which applies minor geometric distortions, followed by a random frequency deviation based around the centre of the image and finally a transfer function to introduce error into all sample values similar to the effects of a scanner. StirMark can serve as a benchmark for image watermarking.
The echo hiding technique encodes zeros and ones by adding echo signals distinguished by different values for their delay and amplitude to an audio signal. Decoding can be done by detecting the initial delay using the auto-correlation of the cepstrum of the encoded signal but this technique can also be used as an attack.
If the echo can be detected then it can be removed by inverting the formula used to add it. The difficult part is detecting the echo without any knowledge of the original or the echo parameters. This problem is known as ‘blind echo cancellation’. Finding the echo can be done using a technique called cepstrum analysis.
Other attacks will attempt to identify the watermark and then remove it. This technique is particularly applicable if the marking process leaves clues that help the attacker gain information about the mark. For example an image with a low number of colours, such as a cartoon image, will have sharp peaks in the colour histogram. Some marking algorithms split these and the twin peaks attack takes advantage of this to identify the marks which can then be removed.
Presentation Attacks: Presentation attacks modify the content of the file in order to prevent the detection of the watermark. The mosaic attack takes advantage of size requirements for embedding a watermark. In order for the marked file to be the same size as the original the file must have some minimum size to accommodate the mark. By splitting the marked file into small sections the mark detection can be confused. Many web browsers will draw images together with no visible split enabling the full image to be effectively restored while hiding the mark. If the minimum size for embedding the mark is small enough the mosaic attack is not practical. This attack can defeat web crawlers which download pictures from the Internet and check them for the presence of a client’s watermark.
Interpretation Attacks: Interpretation attacks involve finding a situation in which the assertion of ownership is prevented. Robustness is usually used to refer to the ability of the mark to survive transformations and not resistance to an algorithmic attack. Therefore the definition of robustness may not be sufficient.
One interpretation attack takes advantage of mark detection being unable to tell which mark came first if multiple marks are found. If the owner publishes a document, d + w (where d is the original and w is the watermark) a pirate can add a second watermark w’ and claim that the document is his and that the original was d + w - w’. Though it is clear that at least one party has a counterfeit copy, it is not clear which one. This would seem to suggest the need to use other techniques to identify the original owner of a file.
Implementation Attacks: As with other areas in computer security the implementation of a marking system can provide more opportunities for attack than the marking technique itself. If the mark detection software is vulnerable it may be possible for attackers to deceive it.
Digimarc, one of the most widely used picture marking schemes was attacked using a weakness in the implementation. Users register an ID and password with the marking service. A debugger was used to break into the software which checks these passwords and disable the checking. The attacker can change the ID and this will change the mark of already marked images. The debugger also allowed bypassing of checks to see if a mark already existed and therefore allowed marks to be overwritten.
There is a general attack on mark readers which explores an image on the boundary between no mark having been found and one being detected. An acceptable copy of the image can be iteratively generated which does not include the mark.
Clearly the software used to implement steganographic techniques needs to be secure and ideas from other areas of computer security can be used to ensure this.
Text 5. Radio Frequency Identification (RFID) I.Radio Frequency Identification (RFID) is a type of automatic identification system. The purpose of an RFID system is to enable data to be transmitted by a portable device, called a tag, which is read by an RFID reader and processed according to the needs of a particular application. The data transmitted by the tag may provide identification or location information or specifics about the product tagged, such as price, color, date of purchase, etc. The use of RFID in tracking applications first appeared during the 1980s even though RFID was developed by allied forces in WWII so radar operators could distinguish between friendly and enemy aircraft. A basic RFID system consists of three components: an antenna or coil, a transceiver (with decoder), a transponder (RF tag) electronically programmed with unique information. When an RFID tag passes through the electromagnetic zone, it detects the reader’s activation signal. The reader decodes the data encoded in the tag’s integrated circuit (silicon chip) and the data is passed to the host computer for processing. Principal areas of application for RFID that can be currently identified include: transportation and logistics, manufacturing and processing, security. The basic feature of an RFID system is the automatic identification of items. In its simplest form, such identification can be binary, e.g., paid or not paid, useful for alerting. Modern tags allow hundreds of bits to be used for such an ID. There are four RFID use cases – alerting, monitoring, identification, and authentication – each can be subverted by a specific type of attack. 1. Authentication and Counterfeiting. Today, RFID-based smart-cards are already in widespread use as payment and travel systems, access control systems and most recently as national and international identification documents. In all cases, it is imperative that the authenticity of the RFID tag cannot be compromised. The widespread availability of writable or even reprogrammable tags means that the use of RFID alone does not offer enough protection from determined counterfeiters. 2.Identification and Sniffing.The core RFID privacy problem is that of unauthorized tag readout: with the help of wireless communication, third parties can in principle read the tags of personal items from large distances, and without any indication that such a readout is taking place. For example, we use RFID in travel documents, where a passport might disclose the citizenship of its bearer and thus allow the hacker to track its bearer. Clearly, this act of sniffing out the data on an RFID tag can only be prevented if tags disclose their identity only to authorized readers, i.e., those that are under the control of the item owner or another authorized party. 3.Monitoring and Tracking.It is important to realize that privacy can also be violated without actually identifying individual items. Once a specific tag or a set of tags can be associated with a particular person, the mere presence of this tag in a particular reader field already implies a location disclosure. And thus tags must either frequently update their ID in a non-predictable manner, or remain completely silent upon inquiries from illegitimate readers. 4.Alerting and Denial of Service.In its simplest form, an RFID tag simply announces its presence, e.g., to an anti-theft gate in a bookstore. Sold items get their embedded RFID tag killed at checkout so that only unpaid items will be detected. Current industry protocols already require compliant tags to offer a Kill-command that completely silences the tag once issued. Tag silencing offers significant privacy gains, yet it directly conflicts with many commercial security concerns, such as theft. A personal jamming device that prevents readers from “coming through” might work quite well.
II.Let’s classify the attacks which are possible to apply to RFID tags. We’ll divide them into 5 categories: 1. Physical Layer attacks. The physical layer in RFID communications is comprised of the physical interface and the RFID devices. This layer includes attacks that permanently or temporarily disable RFID tags as well as relay attacks. They are such attacks as Kill-command, passive interference, active jamming and relay attacks. 2. Network - Transport Layer attacks. This layer includes all the attacks that are based on the way the RFID systems are communicating and the way that data are transferred between the entities of an RFID network (tags, readers). It includes attacks on tags (cloning, spoofing), reader attacks (impersonation, eavesdropping) and network protocol attacks. 3.Application Layer attacks. This layer includes all the attacks that target information related to applications and the binding between users and RFID tags. Such attacks employ unauthorized tag reading, modification of tag data and attacks in the application middleware such as buffer overflows and malicious code injections. 4. Strategic Layer attacks. This layer includes attacks that target organization and business applications, taking advantage the careless design of infrastructures and applications. More specifically this layer includes competitive espionage, social engineering, privacy and targeted security threats. 5. Multilayer Attacks. A lot of attacks that target RFID communication are not confined to just a single layer. In this category attacks affect several layers including the physical, the network-transport, the application and the strategic layer. In particular this layer includes covert channels, denial of service, traffic analysis, crypto and side channel attacks. Now we discuss possible ways to counter these attacks. In order to safeguard RFID systems against low-tech attacks such as permanently or temporarily disabling tags, traditional countermeasures should be used, such as increased physical security with guards, locked doors and cameras. Unauthorized use of KILL commands could be prevented, for example, with effective password management. For the protection against relay attacks possible approaches could be the encryption of the RFID communication or the addition of a second form of authentication such as a password or biometric information. However, this requirement definitely eliminates the convenience and advantages of RFID communication. Through appropriate data collection, it is possible to detect cloned RFID tags. Alternatively, cloning attacks can be mitigated via challenge response authentication protocols. These should also support robust anti-brute force mechanisms. In order to defend against passive eavesdropping attacks encryption mechanisms could be used to encrypt the RFID communication. Spoofing and impersonation could be combated by using authentication protocols or a second form of authentication such as one-time passwords, PINs or biometrics. Network protocol attacks could be countered by hardening all components that support RFID communication, using secure operating systems, disabling insecure and unused network protocols and configuring the protocols used with the least possible privileges. In order to defend against unauthorized tag reading and tag modification on the Application Layer, controlling access to RFID tags should be our focus. One approach proposed was the use of aluminum-lined wallets to protect RFID payment cards and e-passports against unauthorized reading. However since the sniffing of confidential data can nevertheless be performed at the time of actual use, the approach does not seem to be very effective. Encryption techniques, authentication protocols or access control lists may provide an alternative solution. More specifically, approaches based on symmetric key encryption, public key encryption, hash functions, mutual authentication or even non-cryptographic solutions such as pseudonyms, have been proposed. Attacks in Strategic Layer Attacks layer can be defended by using any of the countermeasures employed against attacks included in the other layers. More precisely, for privacy and targeted security threats a broad range of technical solutions have been proposed, including killing or temporarily silencing tags, blocking access to unauthorized readers, relabeling or clipping tags, using pseudonyms, distance measurement and encryption techniques. Covert channels attacks are difficult to detect and defend against. The owners and users of RFID tags have no knowledge that their tags have been compromised and that they are used for a covert channel attack. Foiling these attacks is an open research issue. However, a possible mechanism to combat them should focus on reducing the availability of memory resources in an RFID tag. Denial of Service attacks and traffic analysis are severe security threats in all types of networks including wired. While theoretically these types of attacks can be countered the scarce resources of RFID tags make their defense problematic and remain an open research issue. Crypto attacks can be eliminated through the employment of strong cryptographic algorithms following open cryptographic standards and using a key with sufficient length. Due to the increasingly wider deployment of RFID systems, their security is more critical than ever. In this paper, we tried to discover some structure within the universe of possible attacks that can affect such systems. By considering the point of attack, its systemic effects and countermeasures jointly, we can obtain a more coherent view of the threats and what must be done to counter them. In this paper, we classified attacks based on the layer that each is taking place and we discussed possible countermeasures that can be used to combat these attacks. We discriminated them to attacks deployed in the physical layer, the application layer, the strategic layer and multilayer attacks. Finally, we point out for which attacks further research is necessary in order to achieve adequate defense against them.
MODULE 2. PRESENTATIONS
|
||||
|
Последнее изменение этой страницы: 2016-12-17; просмотров: 208; Нарушение авторского права страницы; Мы поможем в написании вашей работы! infopedia.su Все материалы представленные на сайте исключительно с целью ознакомления читателями и не преследуют коммерческих целей или нарушение авторских прав. Обратная связь - 3.133.143.118 (0.008 с.) |